Identity and Access Management plays a crucial role in reducing the risk of ransomware attacks. Cyber threats continue to advance, and organizations need a structured approach that not only protects systems but also aligns security measures with business priorities and strategy. This requires ongoing alignment between security teams and executive leadership to ensure that cybersecurity initiatives actively contribute to business protection and continuity. It is important to demonstrate how security investments reduce financial exposure and enhance organisational resilience and long-term stability.
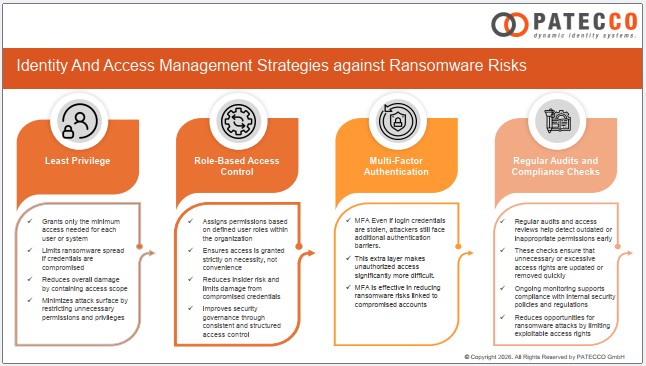
A key element in ransomware prevention is strong identity and access management, which defines how access to systems and data is assigned, controlled, and monitored across the organization. The following measures illustrate how it helps reduce ransomware risks:
- Limiting Access Through Least Privilege Enforcement
The principle of least privilege ensures that users, applications, and systems are granted only the minimum level of access required to perform their tasks. By restricting permissions to the essential minimum, the potential damage of a compromised account is significantly reduced, as attackers can only operate within limited access boundaries. - Role-Based Access Control (RBAC)
RBAC assigns access rights based on defined job roles within the organisation. This structured approach ensures that permissions are granted strictly according to business need rather than convenience. It reduces excessive access, limits insider risk, and minimises the potential impact if credentials are compromised. - Multi-Factor Authentication (MFA)
MFA strengthens access security by requiring users to verify their identity using multiple authentication factors. This additional layer makes it significantly harder for attackers to gain access, even if credentials are stolen, and helps prevent ransomware propagation through compromised accounts. - Regular Audits and Compliance Checks
Ongoing monitoring and periodic audits of access rights ensure that outdated or inappropriate permissions are identified and corrected promptly. This process supports compliance with security standards while reducing opportunities for attackers to exploit unnecessary or excessive access rights. - Automated Provisioning and Deprovisioning
Automated identity management systems ensure that access rights are updated quickly when roles change or are removed immediately when employees leave the organisation. This reduces the risk of lingering accounts and helps prevent unauthorized access points that could be exploited by ransomware attacks. - Segregation of Duties (SoD)
SoD ensures that no single individual has complete control over critical processes. By separating responsibilities, it reduces the risk of misuse of access privileges and limits the potential for ransomware to be introduced into sensitive systems. - User Behavior Analytics (UBA)
UBA enhances identity governance by identifying unusual or abnormal user activity that may indicate compromised accounts or insider threats. Early detection of such behaviour enables timely intervention before incidents escalate into data breaches or ransomware attacks. - Security Monitoring and Incident Response Readiness
Even with strong preventive measures in place, organisations must be able to detect and respond to security incidents quickly. Effective monitoring and response capabilities ensure that suspicious activity is identified early and contained before it can escalate into a serious security breach.
Effective protection against ransomware is possible through a comprehensive and well-coordinated identity and access strategy. When principles such as least privilege, role-based access control, strong authentication, continuous monitoring, and automated lifecycle management are consistently applied, organizations significantly reduce their attack surface and improve overall resilience.
In essence, it is the combination of strong governance, smart technology, and continuous oversight that enables organizations not only to defend against ransomware threats, but also to build a secure and sustainable digital foundation for the future.
For more information, click on the presentation below: