Privileged Access Management (PAM) plays a critical role in modern cybersecurity, supporting Zero Trust strategies, ransomware prevention, and compliance with frameworks such as NIS2 and ISO 27001. Yet, despite significant investments, many organizations struggle to fully realize the value of PAM. Projects stall, adoption remains low, and security teams often manage complex systems that deliver limited risk reduction. While implementing an effective PAM strategy can be challenging, the benefits of securing privileged accounts and credentials significantly outweigh the challenges. This article outlines practical approaches to overcoming common PAM implementation challenges, helping organizations strengthen their security posture and reduce exposure to critical breaches.
Common PAM Implementation Challenges
Implementing PAM comes with a range of challenges that can impact security, usability, and compliance. Understanding these common obstacles helps organizations plan and execute successful deployments.
1. Unclear Strategy and Implementation Plan
Many organizations deploy PAM solutions without fully understanding their privileged access requirements. Skipping essential steps, such as identifying all privileged accounts, conducting access discovery, and performing risk analysis, can result in misaligned priorities and ineffective deployments. Without a clear assessment of the current environment, it is difficult to address vulnerabilities, define a PAM roadmap, or measure success post-implementation.
2. Complicated PAM Infrastructure
Complexity is a leading reason PAM projects fail. Gartner research shows over half of IT teams never fully implement PAM, often due to overly complex architectures. Legacy platforms – built over time with multiple components like endpoint agents, jump servers, session proxies, credential vaults, and custom integrations – become harder to manage as environments grow. Adding cloud, hybrid systems, third-party vendors, and non-human identities can shift focus from enforcing least privilege, turning PAM into a maintenance burden rather than a security tool.
3. Integration Challenges
Integrating PAM into diverse IT ecosystems remains a significant hurdle. CISOs must evaluate the compatibility of their chosen PAM solution with existing infrastructure to ensure seamless implementation without disrupting critical operations. Careful planning and assessment are key to avoiding costly integration issues.
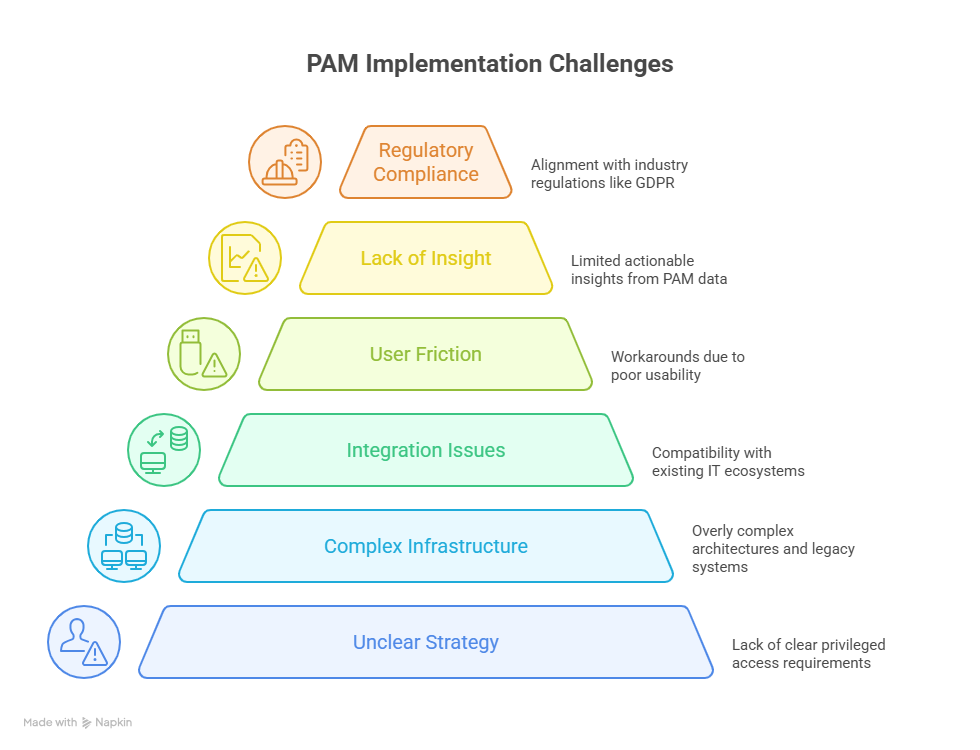
4. User Friction and Limited Adoption
If PAM slows down engineers, administrators, or DevOps teams, they will find workarounds – shared credentials, standing privileges, or hard-coded secrets – that reintroduce the very risks PAM is meant to eliminate. Poor usability, rigid workflows, excessive prompts, and unfamiliar tools can reduce adoption and erode trust between security and operational teams.
5. Poor Transparency and Lack of Insight
Some PAM platforms generate large volumes of data but offer limited actionable insights. Teams may know access occurred but lack context on session behavior or risk exposure. Privileged access gaps are a frequent finding in failed ISO 27001 audits, often linked to excessive standing privileges or insufficient session monitoring. Without meaningful visibility, PAM becomes a compliance checkbox rather than a strategic security control.
6. Adherence to Regulatory Standards
Compliance with regulatory requirements is essential for modern cybersecurity. PAM solutions must align with industry regulations such as GDPR and NIS2. Non-compliance can result in fines, legal consequences, and reputational damage. Selecting and implementing PAM platforms that facilitate regulatory adherence is therefore not optional – it is a necessity.
Strategies for Mitigating PAM Implementation Risks
Effective PAM implementation requires more than technology – it demands a strategic, organization-wide approach. Here’s how CISOs can mitigate common risks and ensure success:
- Develop a Holistic Strategy
Define the scope, objectives, and expected outcomes of your PAM initiative. A clear roadmap ensures alignment with security goals and guides the organization through complex deployments.
- Secure Support Across the Organization
Successful PAM adoption requires executive sponsorship and end-user buy-in. Engage stakeholders early, demonstrate the value of zero-trust security, and consider user needs during deployment.
- Choose a Flexible, Scalable Solution
Select a PAM platform that adapts to on-prem, hybrid, or cloud environments. Scalability ensures it can grow with your organization, manage increasing privileged accounts, reduce insider risks, and streamline operations.
- Leverage Automation
Automate onboarding, offboarding, password rotation, and auditing. Automation reduces IT workload, enforces consistent policies, speeds up access management, and ensures audit readiness.
- Provide User Training
Equip users with practical and technical knowledge of PAM. Effective training highlights productivity benefits, reduces resistance, and positions PAM as a supportive security tool rather than a compliance burden.
By combining strategic planning, executive support, flexible technology, automation, and user education, organizations can overcome PAM implementation hurdles and maximize security and operational efficiency.
How PATECCO simplifies PAM implementation?
Implementing PAM can be complex, but PATECCO streamlines the full lifecycle – from planning to ongoing management. PATECCO simplifies PAM by delivering a tailored strategy, seamless integration, and user-friendly design, leveraging automation to boost efficiency, and ensuring compliance with global regulations and standards such as ISO 27001, NIS2, and GDPR. With PATECCO, organizations can overcome PAM complexity, accelerate deployment, increase adoption, and achieve robust security and operational efficiency.
