In the modern cyber environment, where threats change quickly and regulations are stricter than ever, managing risks proactively is essential. Effective risk management helps organizations identify and mitigate threats, ensure regulatory compliance, protect critical data, and maintain business continuity. By addressing vulnerabilities before they escalate, organizations can make informed decisions and strengthen their overall security framework.
What is Cybersecurity Risk Management?
Cybersecurity risk management is the practice of identifying, evaluating, and addressing potential threats and vulnerabilities to safeguard an organization’s digital assets. A key element of this process is taking proactive measures to prevent incidents before they can compromise systems. By applying structured risk assessment techniques, organizations can understand the potential impact of different threats and prioritize their mitigation efforts effectively.
Security controls are central to risk management, acting as protective measures that reduce vulnerabilities and neutralize threats. Well-executed cybersecurity risk management not only protects sensitive data but also ensures business continuity and maintains stakeholder confidence.
What are the key stages of cybersecurity risk management?
Cybersecurity risk management follows a structured process that includes recognising potential risks, creating mitigation plans, deploying security measures, and continuously monitoring systems for emerging threats. Preventive risk management focuses on deploying protective measures such as firewalls, encryption, access management, and timely software updates to reduce vulnerabilities. Ongoing surveillance of network traffic, system logs, and user activity is critical for quickly identifying suspicious actions or unauthorised access.
Effective incident response requires organisations to maintain a clear, well-documented plan to manage and contain security incidents. This includes activating a specialised response team, isolating compromised systems, and conducting forensic analysis to determine the scope and impact of the breach.
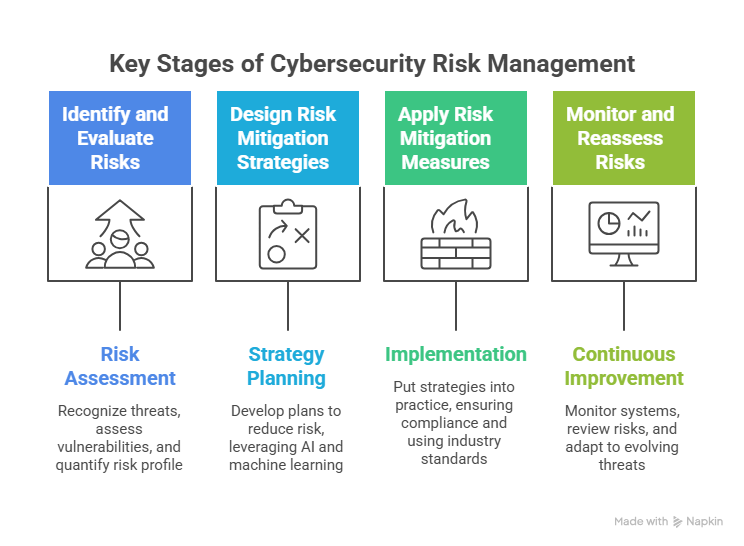
1. Identify and Evaluate Risks
This stage focuses on recognising potential threats, assessing system vulnerabilities, and analysing the organisation’s overall risk profile. Threat modelling helps map possible attack paths and attacker motives, while vulnerability scans uncover weak points in systems or software. Risks are then quantified by likelihood and impact, allowing organisations to prioritise which threats to address first.
2. Design Risk Mitigation Strategies
At this stage, organisations create plans to reduce risk, often leveraging AI and machine learning. These technologies detect unusual activity in real time, automate routine security tasks, and provide predictive insights into potential attacks. This proactive approach helps prevent breaches and allows security teams to focus on more complex threats, reducing the chance of human error.
3. Apply Risk Mitigation Measures
Implementation involves putting strategies into practice while following industry standards, regulations, and third-party risk assessments. Compliance ensures accountability and transparency, and assessing external vendors helps manage additional risks. Using ISO frameworks and best practices strengthens security controls, protects sensitive data, and builds trust with stakeholders.
4. Monitor and Reassess Risks
Continuous monitoring ensures threats are detected early, especially in cloud and supply chain environments. Regular reviews and risk assessments help improve incident response, adapt to evolving threats, and maintain organisational resilience. This stage also promotes a culture of cybersecurity awareness among employees, reinforcing the organisation’s overall defence.
What Are the Advantages of Cybersecurity Risk Management?
Cybersecurity risk management is a critical practice that enables organizations to safeguard themselves against cyberattacks, data breaches, and other forms of cybercrime. Implementing a structured risk management approach offers several key advantages:
- Regulatory Compliance
Organizations are often required to adhere to cybersecurity standards set by regulations such as GDPR, HIPAA, NIS2 and DORA. A comprehensive risk management framework helps ensure these compliance requirements are consistently met.
- Enhanced Decision-Making
Understanding potential risks and their consequences allows organizations to make informed decisions that integrate cybersecurity considerations. This supports more effective resource allocation and system design choices.
- Strengthened Security
By identifying and addressing potential threats, risk management reduces the likelihood of cyberattacks and mitigates their impact if they occur. Organizations can adopt proactive measures to protect critical systems and sensitive data.
- Improved Visibility
Risk management provides a clearer view of an organization’s cybersecurity posture, highlighting areas where additional controls may be needed. This enables better awareness of vulnerabilities and preparedness for emerging threats.
- Optimized Security Strategy
Focusing on the risks with the greatest potential impact allows organizations to prioritize their security efforts and deploy resources more efficiently, resulting in a more streamlined and effective cybersecurity strategy.
