As more organizations embrace digital transformation, the shift toward multi-cloud environments has become a strategic move – enabling businesses to tap into the strengths of multiple cloud providers while avoiding vendor lock-in and enhancing agility. But with greater flexibility comes greater complexity, especially when it comes to securing systems, data, and applications spread across different platforms. Unlike single-cloud environments, where governance and control are more centralized, multi-cloud setups often lead to fragmented visibility, inconsistent security policies, and increased chances of misconfiguration. These challenges, if left unaddressed, can expose an organization to significant risks ranging from data breaches to compliance violations.
In this article, we will highlight the most common security risks in multi-cloud environments and explore actionable strategies to overcome them – helping you build secure, resilient, and well-governed multi-cloud architecture.
- What Are the Typical Security Risks in Multi-Cloud Environments?
While the multi-cloud approach offers undeniable advantages – such as avoiding vendor lock-in, optimizing costs, and increasing service availability – it also introduces a more intricate and often fragmented security landscape. Unlike single-cloud deployments, where policies, tools, and access controls can be uniformly applied, multi-cloud environments require organizations to manage multiple platforms, each with its own security model, interface, and operational nuances.
This increased complexity often leads to gaps in visibility, inconsistencies in security policies, and a broader attack surface. If not managed properly, these challenges can significantly increase the risk of cyberattacks, data loss, and compliance violations.
Here are the top five security risks most commonly encountered in multi-cloud environments:
1. Inconsistent Identity and Access Management (IAM)
Managing user identities and access permissions across different cloud platforms can result in inconsistent policies, over-privileged accounts, and difficulty in enforcing the principle of least privilege. Attackers often exploit weak or mismanaged IAM systems to gain unauthorized access to sensitive resources.
2. Misconfigurations and Human Error
Each cloud provider has its own configurations and default settings. Without standardized configuration practices, there’s a high risk of accidentally exposing resources—such as unsecured storage buckets, open ports, or overly permissive roles—to the public internet or unauthorized users.
3. Lack of Centralized Visibility and Monitoring
With resources spread across multiple cloud platforms, security teams often struggle to maintain full visibility into system activity, threats, and compliance status. This fragmented view makes it difficult to detect anomalies or respond quickly to incidents.
4. Data Security and Compliance Challenges
Data is often transferred and stored across multiple environments, which increases the risk of exposure, loss, or non-compliance with industry regulations. Ensuring data is encrypted, tracked, and compliant across all platforms can be difficult without centralized control.
5. Vendor Lock-In and Integration Gaps
Relying on proprietary tools and services from individual cloud providers can lead to vendor lock-in, making it difficult to migrate workloads or unify security controls across platforms. Many native security tools are not designed to work across different clouds, creating integration gaps and operational silos. This fragmentation leads to inconsistent security policies, duplicated efforts, and limited visibility. Over time, it increases complexity, reduces agility, and elevates risk in managing the multi-cloud environment.
- How to Overcome Security Risks in Multi-Cloud Environments
Securing a multi-cloud environment requires more than just extending traditional security practices to multiple platforms – it demands a cohesive, strategy-driven approach. With data, workloads, and access points spread across different cloud providers, the attack surface expands, and misalignments in security policies can easily occur. To reduce risk, organizations must focus on visibility, consistency, and automation across their entire cloud footprint. Below are five actionable tips to help you build a more secure and resilient multi-cloud architecture.
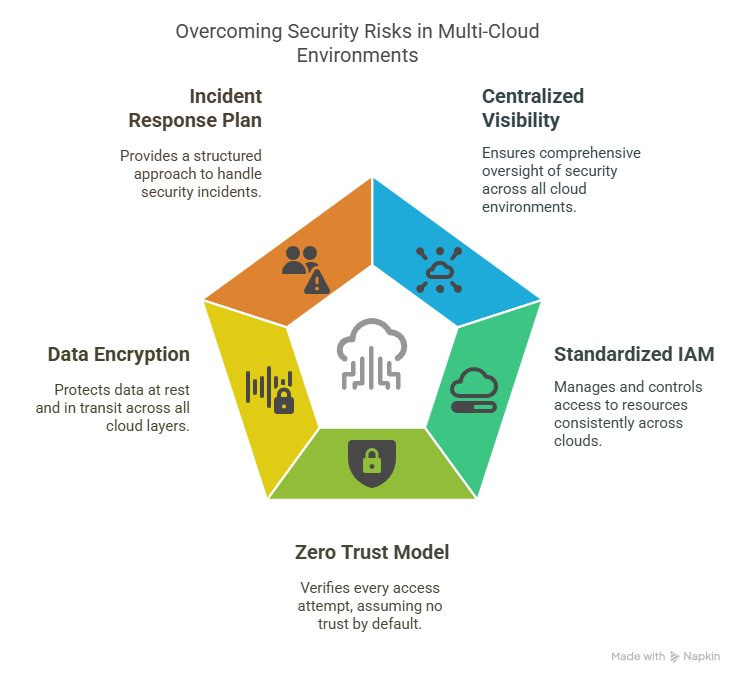
1. Centralize Visibility and Monitoring
Leverage cross-cloud security dashboards and API integrations to unify monitoring across all platforms. Aggregating logs, metrics, and events into a centralized SIEM system enables faster detection of anomalies and suspicious activity. Real-time alerts and correlation across environments help identify threats that may otherwise go unnoticed. Visibility is the foundation of effective multi-cloud security.
2. Standardize Identity and Access Management (IAM)
Implement identity federation and single sign-on (SSO) to manage access across cloud providers under one policy framework. Enforce least-privilege principles using role-based access controls (RBAC) and regularly review user permissions. Avoid using separate IAM configurations for each platform, which increases risk. A unified IAM strategy simplifies governance and limits attack vectors.
3. Implement a Zero Trust Security Model
Adopt a Zero Trust approach where no user or system is inherently trusted, even inside the network perimeter. Continuously verify identities, enforce granular access controls, and monitor user behavior across all cloud platforms. Combine this with micro-segmentation to limit lateral movement in case of a breach. Zero Trust helps contain threats and reduces the blast radius of potential attacks.
4. Encrypt Data Across All Layers
Ensure encryption is applied to data both in transit and at rest using the native encryption tools provided by each cloud platform. Regularly rotate encryption keys and apply strict access controls to maintain the confidentiality and integrity of sensitive data. Be cautious of exposing data during transfers between clouds by using secure protocols. Encryption adds an essential layer of protection, especially when data is distributed across different services.
5. Establish a Multi-Cloud Incident Response Plan
Develop an incident response strategy that covers all cloud platforms, with clear roles, escalation paths, and automated playbooks. Integrate cloud-native tools with centralized response systems to accelerate containment and recovery. Run regular simulations to test the plan’s effectiveness in multi-cloud scenarios. A fast, coordinated response minimizes the impact of any breach.
Securing a multi-cloud environment doesn’t have to be overwhelming. By understanding the typical risks – ranging from misconfigurations to identity sprawl – and implementing proactive, unified, and automated security practices, organizations can confidently harness the power of multi-cloud without sacrificing their security posture.
