Organizations today operate in a business environment where cyber risks evolve faster than internal defenses can adapt. From ransomware and phishing attacks to insider threats and compliance violations, businesses face continuous exposure that can disrupt operations, destroy trust, and lead to regulatory penalties.
In this environment, cybersecurity audits have become a fundamental component of effective risk management. A well-executed audit enables organizations to identify vulnerabilities before they are exploited and provides leadership with the transparency needed to make informed, strategic security decisions.
Who needs a cybersecurity audit?
Any organization that manages sensitive information, no matter its industry or scale, should be concerned. Small and medium-sized enterprises, large corporations, industrial firms, and finance and healthcare institutions alike can all become targets of cyberattacks. A cybersecurity audit delivers critical visibility into existing risks and how they should be managed. Without this clarity, organizations rely on assumptions rather than detailed insights.
A comprehensive audit helps organizations to:
- Detect technical vulnerabilities
- Verify the effectiveness of security controls
- Minimize regulatory and compliance risks
- Enhance incident response capabilities
- Strengthen governance frameworks
As a result, cybersecurity becomes measurable, manageable, and aligned with business objectives. Audits also play a key role in validating and refining cybersecurity strategies. They encourage organizations to critically assess their current state by addressing questions such as:
- How up to date are our cyber risk management plans?
- Do they reflect recent incidents and emerging threats?
- Are all business units aligned with current security requirements?
- Have outdated technologies been replaced?
- Are updates and patches applied consistently?
What Does a Cybersecurity Audit Actually include?
Modern cybersecurity audits extend far beyond basic vulnerability scans. They provide a holistic evaluation of an organization’s security posture across technology, processes, and people.
Key areas typically include:
- Data Security: Assessment of access controls, encryption standards, and data protection in transit and at rest
- Operational Security: Review of policies, procedures, and governance structures
- Network Security: Evaluation of monitoring capabilities, configurations, and threat detection mechanisms
- System Security: Analysis of system hardening, patch management, and privileged access controls
- Physical Security: Examination of safeguards such as multi-factor authentication, biometric controls, and device protection
This comprehensive approach ensures that security is not viewed in isolation, but as an integrated, organization-wide capability.
Best Practices for Audit Preparation
Effective preparation is essential to ensure a smooth and valuable audit process. Well-structured documentation and clear processes enable auditors to assess security controls efficiently and accurately.
Key preparation steps include:
- Review data security policies to ensure protection of confidentiality, integrity, and availability
- Centralize cybersecurity policies to provide a clear and consistent overview
- Document network architecture to give auditors full visibility into systems and dependencies
- Align with relevant compliance frameworks to ensure audit relevance
- Define roles and responsibilities within the security team to support efficient evaluation
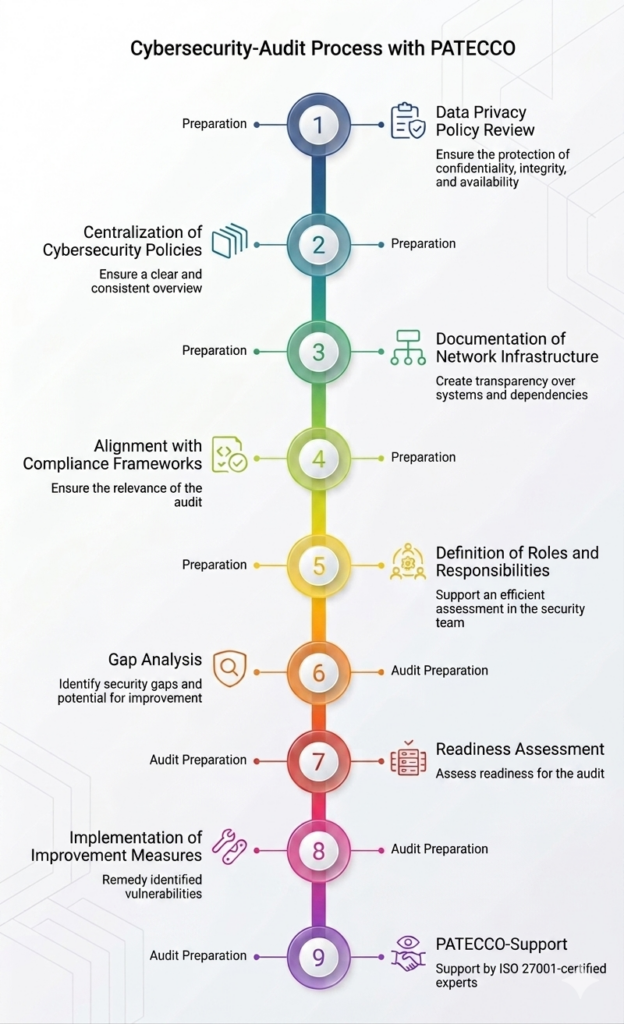
Source: AI-Generated infographic
How Cybersecurity Audits Build Stronger Business Protection?
Cybersecurity audits play a key role in strengthening an organization’s overall security posture. By systematically identifying vulnerabilities, assessing risks, and evaluating existing controls, they provide a clear foundation for improving defenses. This proactive approach helps businesses reduce exposure to threats and build more robust protection for their systems, data, and operations.
The outcome is clear – improved compliance with regulatory requirements, increased customer and partner trust, faster detection and response to threats, reduced operational and financial impact of incidents, enhanced visibility into security risks and vulnerabilities and stronger alignment between security and business objectives.
How can PATECCO support you for a successful audit?
As an ISO 27001 certified consulting company, PATECCO helps organizations prepare effectively for cybersecurity and compliance audits by strengthening their information security management systems and identifying key risks early on.
Their experts support the full audit process – from GAP- analysis and readiness assessments to implementing improvements – ensuring compliance with international standards and a strong security posture. With cross-industry experience and tailored solutions, PATECCO simplifies complex audit requirements and increases your readiness and confidence for a successful audit outcome.
