Energy companies are increasingly targeted by ransomware, APTs, and DDoS attacks. Industrial Control Systems (ICS), SCADA, and IoT networks are especially vulnerable, exposing utilities to serious operational and financial risks. Aging infrastructure, complex IT/OT environments, and regulatory requirements like NIS2 Directive make cybersecurity even more challenging. Extreme weather and targeted attacks increase the likelihood of disruptions and data breaches. The consequences are serious: outages can cause revenue loss, reputational damage, and regulatory penalties.
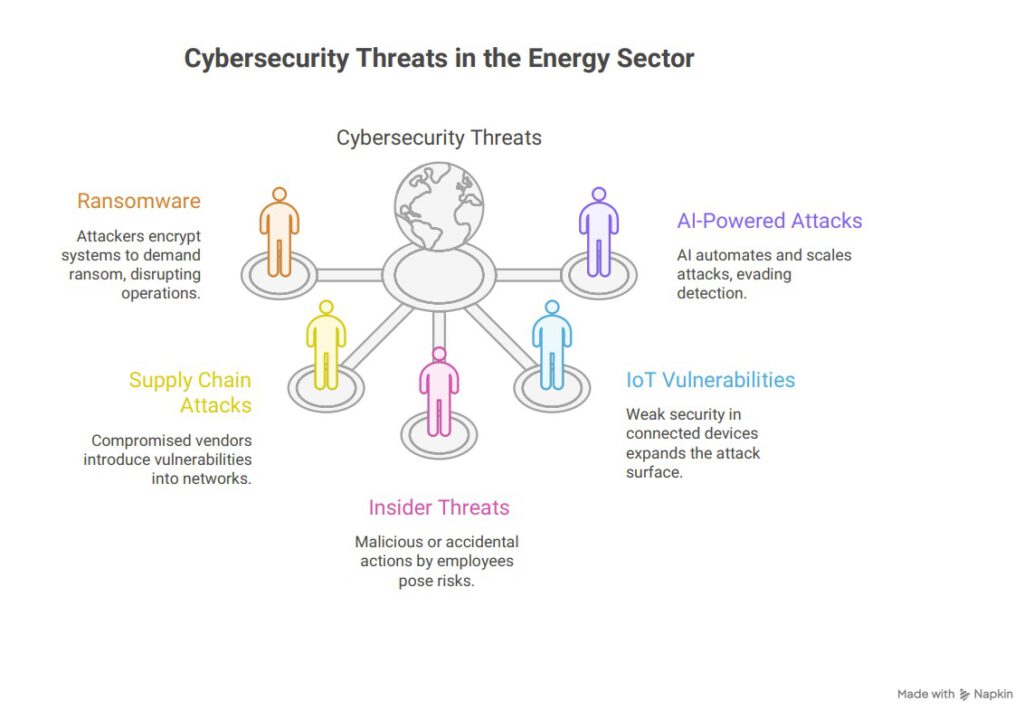
Key Cybersecurity Threats Facing the Energy Sector
As energy companies adopt digital technologies and connect more devices to their networks, cybercriminals have new opportunities to exploit vulnerabilities. Threat actors are not only targeting IT systems, but are increasingly focused on operational technology, smart grids, and the human factor as well. Understanding the most pressing threats is essential to building resilient energy infrastructure and protecting critical services. Some of the key cyber risks are:
- Ransomware: Attackers encrypt operational and business systems to demand ransom, often targeting energy providers due to their critical role in society. Beyond financial loss, ransomware can halt production, disrupt SCADA and ICS systems, and compromise safety protocols.
- Supply Chain and Third-Party Vendor Attacks: Compromised vendors or contractors can introduce hidden vulnerabilities into energy networks, enabling attackers to bypass direct defenses and access sensitive systems indirectly. Companies must carefully assess third-party partners and continuously monitor supply chain connections to reduce these risks.
- Insider Threats and Credential-Based Attacks: Whether malicious or accidental, insider actions and stolen credentials pose high risks. Attackers can gain unauthorized access, manipulate systems, or exfiltrate sensitive data without triggering alerts. Implementing strict access controls, monitoring user behavior, and enforcing regular credential reviews can help mitigate these threats.
- IoT and Smart Grid Vulnerabilities: Connected devices and smart meters expand the attack surface. Weak security in IoT components can allow attackers to manipulate grid operations, disrupt energy distribution, or harvest operational data. Regular updates, device authentication, and network segmentation are critical to safeguarding IoT and smart grid systems. Regular updates, device authentication, and network segmentation are critical to safeguarding IoT and smart grid systems.
- AI-Powered Attacks: Artificial intelligence enables attackers to automate and scale attacks, evade detection, and exploit system weaknesses with unprecedented speed. AI-driven threats can mimic legitimate users, launch sophisticated multi-stage attacks, and overwhelm traditional security measures.
How to build cyber resilience?
1. Comprehensive Risk Assessments for Energy Infrastructure
Effective risk management starts with understanding critical assets and risks. Assessments identify key systems, evaluate threats, review controls, and estimate impact. They must also consider physical consequences, grid stability, and cascading failures. Scenario-based approaches show how attacks may develop step by step. This helps prioritize the most critical risks and focus investments where they have the greatest impact.
2. Building a Cybersecurity Maturity Framework
A maturity framework provides a structured path to improve security over time. Organizations progress step by step, building core capabilities before adding advanced controls. Frameworks should align with standards like NIST and reflect energy-specific needs. Assessments identify gaps, set priorities, and define a clear roadmap. They also help communicate risks in business terms.
3. Strengthening Information Sharing and Collaboration
Cyber threats in the energy sector require collective defense. Sharing information helps detect threats earlier and respond more effectively. Industry platforms enable secure exchange of threat intelligence. Clear guidelines are needed to define what can be shared and with whom. Despite challenges, collaboration improves visibility, response speed, and overall security.
4. Investing in Advanced Security Technologies
The right technologies strengthen security, even though they are not a complete solution. Organizations should choose tools that protect systems without impacting operations. Key solutions include endpoint protection for industrial systems, network monitoring for energy protocols, and automated response tools. Cloud-based services offer scalable and cost-effective options.
How PATECCO Supports You?
PATECCO supports organizations in building and maintaining effective and sustainable information security across both technical and organizational areas. We help assess and implement NIS2 requirements, design and establish management systems such as ISMS and conduct risk assessments, audits, and training. In addition, our managed services ensure continuous security, compliance, and long-term resilience.
